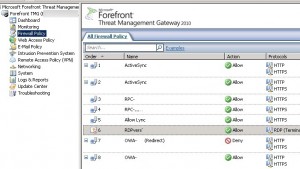
Powershell: Export firewall rules on your TMG servers
In order to manage TMG with powershell you need to use the FPC.root COM object. For more details you can read this article. The purpose of this script is to export for each TMG server the Firewall Policies in XML format:
In order to perform a connection on each TMG server we invoke the ConnectToConfigurationStorageServer method. Then we use the FPCPolicyRules collection in order to browse the different firewall rules. For each TMG server is displayed:
- The rule name.
- Wether the rule is enabled.
- Action: Allow traffic (0), deny traffic (1).

Each firewall rule is exported in the current directory in a file named %TMGSERRVERNAME%_%RULENAME%.xml. In order to export the configuration in XML format we invoke the FPC.ExportToFile method:
$oFPC = New-Object -comObject FPC.root $cArrays = $oFPC.Arrays Foreach ($oArray in $cArrays){ $policyrules = $oArray.ArrayPolicy.policyrules foreach ($policyrule in $policyrules){ $policyrule | select name,enabled,action $szOutFilePath = 'C:\' + $policyrule.name + '.xml' #See options for $iOptionalData at http://msdn.microsoft.com/en-us/library/aa490382.aspx $iOptionalData = 0x00000001 -bor 0x00000002 -bor 0x00000004 -bor 0x00000008 $szPassword = "12345678" $szComment = "" $policyrule.ExportToFile($szOutFilePath, $iOptionalData, $szPassword, $szComment) } } |
Just click on the link below to download the full script:
Change the following default values:
- $servers: TMG server names.
- $iOptionalData: Export type (Radius data…) See this link for more details.
- $szPassword: Password used to encrypt confidential data (e.g. Radius data…)
This post is also available in: French
10 Comments
Other Links to this Post
RSS feed for comments on this post. TrackBack URI

By Divya, May 9, 2012 @ 10:44 pm
Hi,
can you help me with a script to check if a rule is enabled or not?, on a TMG via powershell. I do not want to export the file…if you can tell me the function to display the result and also the defining the policy..thanks so much for ur help..
By ldap389, May 10, 2012 @ 11:01 am
Hi,
The following script checks if the rule named $name exists and checks if it is enabled or not.
$name = “Rule1”
$oFPC = New-Object -comObject FPC.root
$cArrays = $oFPC.Arrays
Foreach ($oArray in $cArrays){
$policyrules = $oArray.ArrayPolicy.policyrules
foreach ($policyrule in $policyrules){
if ($policyrule.name -eq $name)
{if ($policyrule.enabled -eq $true){write-host ‘Policy ‘ $name ‘ is enabled’}
else {write-host ‘Policy ‘ + $name +’ is disabled’}}
}
}
Hope this help.
Regards
By Divya, May 16, 2012 @ 6:37 pm
Hi,
Thanks so much for your help. Sorry did not get time to test it till now. I will let you know..but thanks a lot for prompt reply 🙂
By gate, May 23, 2012 @ 8:27 pm
i had one more TMG question, I am trying to script to find out if remote management system policy rule is enabled.
In the TMG MMC, choose Firewall policy on the Left Pane, in the right Pane select Edit System Policy, select Remote Management –> Terminal Server on the left, on the right select From TAB, double click Remote Management Computers, ensure there is an entry for 10.x.x.x.
i had a way of doing it by getting the sourceselectionIPS in policy rule
http://msdn.microsoft.com/en-us/library/ff825755(v=vs.85)
if you can help me in this…it wud be really really help my job..thanks a lot..
By ldap389, June 1, 2012 @ 7:01 pm
First use this script to retrieve System Rule Information for the rule named “Allow remote management from selected computers using Terminal Server”. This rule has a static GUID {e0093bf3-fa16-4a3c-afe1-19d502ce9608}.
For a list of static GUID in TMG check ftp://222.185.248.37/ISA_%20Server2004_cn/ISA_%20Server2004_cn/sdk/inc/FpcObjectsGuids.h
———————————– Script —————————-
$oFPC = New-Object -comObject FPC.root
$cArrays = $oFPC.Arrays
Foreach ($oArray in $cArrays){
$TSrule = $oArray.SystemPolicy.PolicyRules | where {$_.PersistentName -eq “{e0093bf3-fa16-4a3c-afe1-19d502ce9608}”}
$TSRule
write-host “Allowed Computers Sets for TS management”
$SelectionIPs = $TSRule.SourceSelectionIPs
foreach ($SelectionIP in $SelectionIPs){
$SelectionIP
$cpus = $SelectionIP.ComputerSets
foreach($cpu in $cpus){$cpu}}
}
————————————————
Check the result in result1.jpg attached. Check the Enabled value, then browse the SourceSelectionIPs, and inside this browse the “ComputerSets”. Check that “Remote Management Computers” is present.
Now you need to check what’s inside the “Remote Management Computers” computerset, this built in computer set has a guid of {BECD4ACD-70F7-484D-A161-EA24D887D04F}, use this script to retrieve the computer set:
———————————–Script————–
$FPCRoot = New-Object -ComObject FPC.Root
$Array = $FPCRoot.GetContainingArray()
$addranges = $Array.RuleElements.ComputerSets |where{$_.PersistentName -eq “{BECD4ACD-70F7-484D-A161-EA24D887D04F}”}
$addranges
——————————————————
When you tell me 10.x.x.x is that a specified IP, Subnet, AddressRange? Depending on the answer just browse the values Computers, AddressRanges, Subnets of the $addranges variable with a foreach loop, and here you go 🙂
You can check this link on how list computers in a computer set
http://technet.microsoft.com/en-us/library/bb794719.aspx
Regards
By Ben, June 18, 2012 @ 1:10 pm
This is an awesome script, very useful, however, is there a way to import rules en masse? I’ve made 10 copies of a set of rules and edited them for different domain names, and now want to get them back in. Would editing the entire firewall config and copy-pasting be a better way to go about it?
By ldap389, June 18, 2012 @ 3:26 pm
You can try to import the rules after modifying the exported XML with the Import from file method. But you can do this if all the rules use the same web listenner and are edited on the same TMG server, because there is information related to those parameters in the XML export. I did not test it, so it might be safer to copy-paste the rules, or test the import in a lab environment if you have one.
By Ben, June 18, 2012 @ 3:40 pm
Thanks for the quick response! I have 10*13 rules to import, so I’d rather avoid copy pasting. I do have a lab, so I’ll give the import method a go. I’ll let you know how I get on…
By utpal, May 6, 2019 @ 11:37 am
Is there any way to fetch Forfront TMG policies in excel through powershell.
By ldap389, March 23, 2020 @ 11:38 pm
I guess with the PowerShell Excel module:
https://devblogs.microsoft.com/scripting/introducing-the-powershell-excel-module-2/